OERu Web Services as of August 2022
In the intervening 17 months since my last update the OER Foundation (OERF) has continued to develop new online services for its global community of learners and educators. All of these services are themselves built with - and hosted on - Free and Open Source Software or FOSS. Each application is the work and responsibility of its own global developer community.
Installing and Upgrading Moodle with Docker Compose on Ubuntu 22.04
Note: work in progress
Moodle is probably (there's little agreement among the pundits) the market-leading Free and Open Source Software (FOSS) Learning Management System (LMS). It's pretty much everywhere. Here's how you can set up and maintain your own Moodle instance(s).
Upgrading a Docker-based Discourse Forum instance
Discourse is the world-leading online web-based forum. It's a superb, extremely mature-and-yet-cutting edge platform. It also happens to be Free and Open Source Software, which is why we, at the OER Foundation, use it.
Like all good software, it's undergoing continuous improvement by its developer community who release fairly frequent - perhaps every couple weeks - updates. Luckily, keeping your Discourse forum up-to-date isn't particularly onerous.
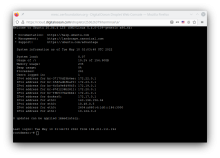
Creating Linux shell users with sudo and SSH access
With Linux servers, both local and in "the Cloud" (aka a Virtual Private Server or VPS), access is generally remote via a command line interface. This tutorial covers the process of creating normal shell (command line) users who have the ability to perform administrative tasks (via the 'sudo' - Super User DO - mechanism), as well as configuring that user to be able to log in from their workstation via SecureShell (SSH) without needing to enter a password (i.e. using public-private key pairs).
Install Rocket.Chat on Ubuntu 20.04 via Docker Compose
This post is a companion to our video tutorial on installing Rocket.Chat 4.x on an Ubuntu 20.04 server via Docker Compose.
We start with a Docker Compose-configured server. You can also see our video tutorials on how to create one: complete, or starting from a DigitalOcean 'snapshot'.
BBB Tutorial Schedule
The schedule for the Samoa Knowledge Society Initiative (SKSI) BigBlueButton Tutorial is as follows:
Before the tutorial
Please create an account on the forum we have set up for the MESC Lifelong Learning Lab. (This free and open source software forum application is powered by Discourse).
Installing BigBlueButton on an OERu Docker Server
This tutorial was developed for the Samoan Knowledge Society Initiative, in which the OER Foundation is very pleased to be involved. (Update 2022-02-10: we have also created a video tutorial based on this written tutorial)
Installing MariaDB on Ubuntu 20.04
At the OER Foundation, we have the convention of using Docker to deploy most components of the web services we offer. One notable exception to that is the way we deploy our most widely used database. Rather than deploying a separate MySQL/MariaDB container for every service on a given host, we instead deploy a single instance running on the host. We do this for a couple reasons:
Creating strong random passwords
Throughout our Free and Open Source Software tutorials, we need to specify passwords for things. Creating random passwords is surprisingly hard, but we've found a method that's very serviceable and makes it easy to do as we all should: ensure every separate identity or service has a strong password that is unique to that identity and application (i.e. never use the same password in more than one place). We also strongly encourage you all to track your passwords using a password manager!
Setting up OERu-style virtual Ubuntu 20.04 or 22.04 server for Docker Compose
Here at the OER Foundation, where we build and maintain the computer services used by the OERu, its learners, and its educators around the globe, we've come up with a tech process that seems to work very nicely, with minimal cost and maintenance overhead. It involves setting up hosting infrastructure to adhere to some conventions that have emerged over time (and are subject to change if we identify better ones).